May 14, 2024
By John Jakovlic
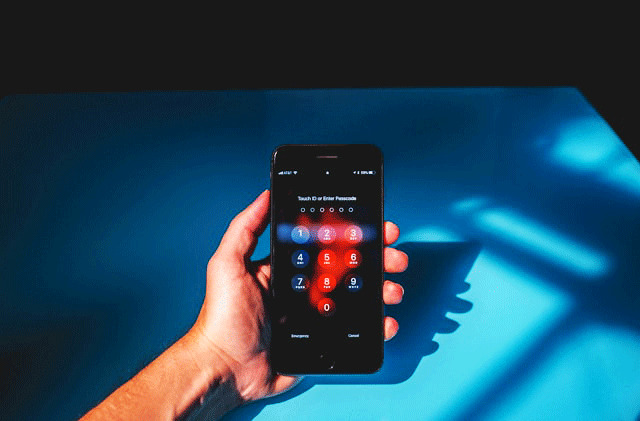
Do I really have to update my password again?
Sure, we’re all tired of managing passwords and it can often feel like a cumbersome task—but the risks of a data security breech outweigh the effort it takes to keep our devices safe and secure.
Smartphones serve as an extension of our professional lives; and as a result, protecting our corporate-owned devices is now a critical part of our job. One of the most fundamental, yet often overlooked, aspects of data security on smartphones is password protection.
As a professional in the mobile phone recycling industry with extensive experience in serving large corporate and government clients, I cannot emphasize enough the importance of taking password security seriously.
All of us work and live in an interconnected world. Smartphones are not merely communication tools—they are repositories of sensitive information, ranging from confidential emails and proprietary documents to client data and financial records. This means that any breach of security on these devices can have far-reaching consequences, including financial loss, damage to reputation, and even legal ramifications.
While I was conducting some research for writing this article I happened upon this alarming infographic developed by Hive Systems that outlines how much time it would take for a hacker to brute force a password based on its complexity. Knowing that most smartphones are only protected by a 4-character numbers only password which can be hacked instantly left me feeling a little uneasy.
Image Source: Hive Systems

Here are several key reasons why securing corporate-owned devices with more robust passwords should be a top priority for every business associate:
- Protection Against Unauthorized Access: Passwords serve as the first line of defense against unauthorized access to sensitive information stored on smartphones. By implementing strong and unique passwords, businesses can significantly reduce the risk of data breaches and unauthorized data access.
- Compliance with Data Protection Regulations: Considering that there are currently 15 states – California, Virginia, Connecticut, Colorado, Utah, Iowa, Indiana, Tennessee, Oregon, Montana, Texas, Delaware, Florida, New Jersey, and New Hampshire – that have comprehensive data privacy laws in place, businesses are obligated to ensure the security and privacy of customer and employee data. Implementing password protection measures on corporate-owned devices is not only good practice but also essential for compliance with these regulations.
- Prevention of Data Theft and Corporate Espionage: Cybercriminals and corporate spies are constantly on the lookout for opportunities to steal valuable corporate data. Weak or easily guessable passwords provide an open invitation for malicious actors to access sensitive information, putting the entire organization at risk.
- Mitigation of Insider Threats: While external threats often receive a lot more attention, insider threats pose a significant risk to data security as well. Disgruntled employees or contractors with access to corporate-owned devices can misuse or leak sensitive information if proper password protection measures are not in place.
- Preservation of Brand Reputation: A data breach resulting from lax password security can tarnish a company's reputation and erode the trust of clients, partners, and stakeholders. Proactively implementing robust password protection measures demonstrates a commitment to safeguarding sensitive information and upholding the highest standards of data security.
While the digital world we work in continues to evolve, one thing remains constant: the importance of prioritizing password security to safeguard corporate-owned devices and sensitive business data. As a trusted partner with two decades of experience in B2B recycling for large corporate and government clients, e-Cycle understands the critical nature of data protection. Beyond implementing robust password security measures, it's equally essential to consider the end-of-life management of mobile devices.
By partnering with e-Cycle for your mobile phone recycling needs, you not only ensure the secure disposal of older devices but also contribute to environmental sustainability. Our tailored solutions prioritize data security at every stage of the recycling process, guaranteeing the safe and responsible handling of sensitive information stored on retired devices. Together, let's fortify your corporation’s data security strength while embracing sustainable practices for a brighter, more secure future. Contact e-Cycle today to learn more about how we can help safeguard your business and the environment simultaneously.
————————————————————————————————
e-Cycle is the trusted wireless partner for many of the largest organizations in the world. As an R2V3 certified organization, we adhere to the highest standards for environmental responsibility and worker health and safety. e-Cycle offers a simple, secure, environmentally responsible and profitable way for businesses to sell and recycle used mobile phones and tablets. Learn more at www.e-Cycle.com.
NOTE: We use cookies on this website. If you continue to access our website, we'll assume that you consent to receiving cookies in accordance with our Privacy Policy.
©2026— e-Cycle. All rights reserved.
Designated trademarks and brands are the property of their respective owners. e-Cycle is not affiliated with the manufacturers of the items available for cash buyback.